You access a Zoom meeting link, and the screen shows a familiar waiting room with the sound of participants joining the meeting one by one. Just a few seconds later, the call starts lagging, a “network issue” notification appears, and an “update available” window pops up with a countdown timer requesting an immediate update. If you click to download, it is highly likely that you have installed monitoring software on your own computer.
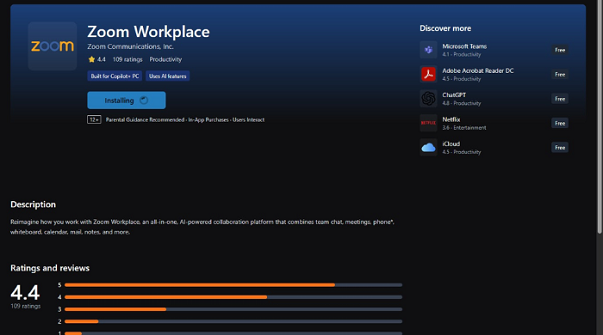
In fact, this is a fake website using unusual domain names such as uswebzoomus[.]com, but designed to look exactly like Zoom’s waiting room in order to deceive users. All sound effects, virtual participant images, and error notifications are staged to create the feeling that a legitimate meeting is experiencing technical problems, forcing users to download a fake update.
Cybersecurity experts say that when this fake update is installed, spyware will silently appear on the computer. It can record keystrokes, take screenshots, and collect user data without showing clearly like normal programs.
According to records from cybersecurity monitoring systems and international analysis reports, in just 12 days of February 2026, this campaign infected 1,437 Windows computers worldwide.
Facing this sophisticated impersonation trick, Bkav recommends:
-
Only open Zoom from the installed application or manually type the correct address zoom.us in the browser; do not access meeting links from unclear sources.
-
Do not download or install any “updates” that suddenly appear on the browser, especially those with countdown timers forcing action.
-
Absolutely do not open files downloaded from unknown websites.
-
When detecting unusual signs, immediately disconnect from the Internet, scan the entire computer for viruses, and change passwords of important accounts using another device that has never accessed the suspicious link.
-
Install email monitoring systems, antivirus software, and comprehensive anti-malware solutions, because built-in software that comes with the operating system is only designed to meet basic protection needs and is not sufficient to defend against ransomware and modern viruses designed to persist long-term and deeply embed in systems.
Bkav





